A case study in the importance of anonymous travel
The case of Rutgers University professor Mark Bray and his family provides an object lesson in the importance of being able to travel anonymously, and how the practices of governments and airlines endanger travelers by making them identifiable.
Dr. Bray, his partner Dr. Yesenia Barragan (also a professor at Rutgers), and their two young children tried to flee the US last month after being denounced by members of the Rutgers chapter of Turning Point USA, doxxed, and receiving death threats. They planned to spend the rest of this academic year teaching remotely from Spain, where Dr. Bray had lived on previous research trips.
Trying to get away from death threats isn’t an uncommon reason for travel, unfortunately. The factors behind the threats against Dr. Bray and his family — Dr. Bray’s scholarship as a historian of anti-fascist activism in Europe and North America since World War II — may be atypical. But thousands of people in the US flee their homes every day to escape from threats or ongoing patterns of domestic violence, often including credible death threats. We’ll never know how many of them have been stalked through their airline reservations.
Dr. Bray and his family bought tickets on United Airlines for a nonstop flight from Newark to Madrid — the most direct route from Rutgers (just a few miles from Newark in New Brunswick, NJ) to Spain. This was, unfortunately, also the most obvious airline and airport for them to use, and the easiest one for any of their local adversaries to stake out.
After they got to the airport, Dr. Bray posted on Bluesky, that, “‘Someone’ cancelled my family’s flight out of the country at the last second. We got our boarding passes. We checked our bags. Went through security. Then at our gate our reservation ‘disappeared.’”
In an interview with the Associated Press from a hotel room where he spent the night before trying again a day later, Prof. Bray said that, “We called the service that made the reservation. They didn’t cancel it. United [Airlines] didn’t cancel it.”
Bary told Mother Jones that airline staff “made a bunch of phone calls and basically said that, somehow, someone at the very last second had canceled our flight reservation—which I didn’t even know was possible.”
Airline staff rebooked the family on the same flight 24 hours later, when they had a different experience. In a later interview after making it to Spain, Dr. Bray described being pulled aside at the departure gate at Newark the next evening by Federal agents for an hour of questioning before being allowed to board the flight to Madrid with his family.
Dr. Bray and his family may never know who cancelled their reservations unless the culprit confesses, but there are two important lessons in this incident:
First, anonymous travel matters, sometimes as a matter of life or death. Both anonymity and the right to travel are never so important as they are for those who are fleeing death threats, whether those threats come from domestic abusers, vigilantes, or the government.
A decision last month by the 9th Circuit Court of Appeals in a case against Lufthansa shows how disclosure of personal information by an airline can put travelers at risk. A gay Saudi Arabian citizen reluctantly provided a copy of his marriage certificate (a same-sex marriage in the US to a US citizen) to Lufthansa. The marriage to a US citizen was relevant to the traveler’s admissibility to the US, but not to the validity of his ticket from Riyadh via Frankfurt to San Francisco, or to Lufthansa’s obligation to transport him. And because homosexuality, as would be conclusively proven by the marriage certificate, is a capital offense in Saudi Arabia, the traveler had not previously disclosed his sexual orientation to the Saudi government. But because Lufthansa staff took actions that may have disclosed his marriage to the Saudi government, he hasn’t dared to return to Saudi Arabia. He has been cut off from his family and community and has been forced to liquidate his real estate there at a loss, among other consequences. The takeaway from the case, at this stage, is that protecting passenger data really can be a life-or-death matter.
Name and ID requirements are touted as measures to “protect” travelers. But for some of the most vulnerable travelers they are a threat to personal security.
We don’t think governments should require passengers on common carriers to identify themselves, or that common carriers should be allowed to require them to do so. On domestic flights in the US, until 1996 anyone could buy a ticket in any arbitrary name and fly without showing any ID. We see no reason not to return to this historic norm.
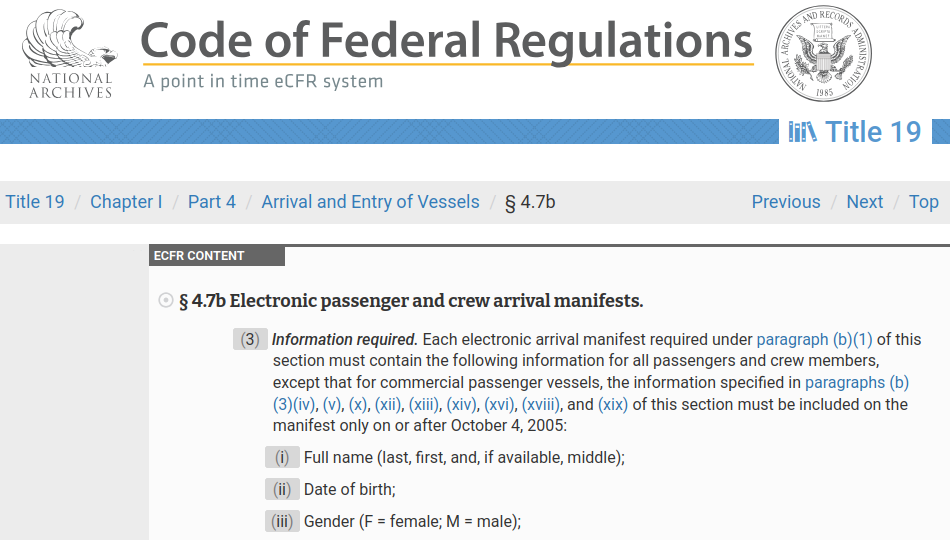
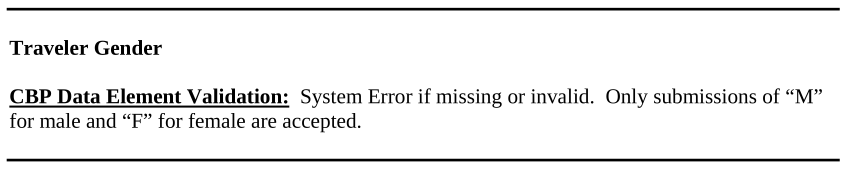
On international flights, passengers’ names and documents may be relevant to decisions made by governments as to their right to leave the country from which the flight departs or to be admitted to the destination country on arrival. But travelers can show their passports or other documents or make their claims for admission without documents (for example, as asylum seekers) without needing to identify themselves to airlines or other private parties. The right to leave any country is, under international treaty law, almost absolute. And decisions about admissibility, particularly in the case of asylum seekers, can be made only after arrival on the territory of the destination country. Airlines have no legitimate need to require identifying information about passengers.
Second, identifying information about air travelers isn’t adequately protected.
If governments unnecessarily require travelers to identify themselves to airlines or other common carriers, then it must be recognized that (1) names and other potentially life-threatening identifying information are provided to these carriers solely to satisfy government mandates, and could not and would not otherwise be required or provided, and (2) the government therefore has the obligation to make sure that this extremely sensitive information is not retained, used, or disclosed to anyone except the government.
As has long been known, and as the experience of Dr. Bray and his family illustrates yet again, airlines have failed to put in place even minimal protections for passenger data, and governments in the US and other countries, including in Spain and the European Union, have failed to require airlines to protect this data or to sanction airlines for not doing so.